Your OTP expires before the user finishes typing. Or worse, it never expires at all, and an attacker walks right through your verification flow.
OTP best practices — expiration windows, rate limits, input UX — determine whether your authentication system is secure, usable, or both. Get them wrong, and you lose users to frustration or lose data to fraud.
This guide covers the OTP expiration time best practices, rate limiting strategies, and UX patterns that separate production-ready OTP systems from vulnerable prototypes. Every recommendation is grounded in NIST SP 800-63B guidelines and real-world implementation patterns.
OTP Expiration Time Best Practices
Expiration is your first line of defense. A stolen OTP with a 30-second window is nearly useless. A stolen OTP with a 30-minute window is a skeleton key.
The stakes are higher than ever. NIST SP 800-63B-4 now classifies SMS OTP as a “restricted authenticator” — meaning it remains acceptable but carries known vulnerabilities (SIM swap, SS7 interception) that demand tighter implementation controls. Short expiration windows are one of the most effective controls you can apply.
Recommended Expiration Windows by Use Case
Not every OTP deserves the same timer. Match the expiration window to the risk level and user context.
| Use Case | Recommended Window | Rationale |
|---|---|---|
| Login / Sign-in | 30 – 60 seconds | Low-friction action, high frequency. Short windows reduce interception risk. |
| Transaction Confirmation | 3 – 5 minutes | User needs time to review transaction details before entering the code. |
| Account Recovery | 10 – 15 minutes | Users may need to switch devices or access a secondary email/phone. |
| Device Registration | 5 – 10 minutes | One-time setup flow, higher friction is acceptable for security. |
| Email Verification | 15 – 30 minutes | Email delivery delays are common. Longer windows prevent unnecessary retries. |
NIST SP 800-63B recommends OTPs remain valid for no longer than 10 minutes for most authentication scenarios, with shorter periods preferred for high-risk operations.
Why Shorter Windows Win
Every extra minute of OTP validity is an extra minute an attacker has to intercept, phish, or brute-force the code.
Shorter windows reduce:
- SIM swap attack risk — Attackers who redirect your user’s SMS have less time to act
- Shoulder surfing exposure — A code seen on a notification is useless if it expires in 30 seconds
- Replay attack potential — Captured OTPs become invalid before they can be reused
The tradeoff is UX friction. If your window is too short, legitimate users get locked out. Monitor your OTP expiration failure rate — if more than 5% of users hit expiration errors, extend the window incrementally.
Handle Expired OTPs Gracefully
Never show “Invalid code” when the real issue is expiration. Your error messaging should distinguish between:
- Wrong code: “That code doesn’t match. You have 2 attempts remaining.”
- Expired code: “This code has expired. We’ve sent a new one to your phone.”
- Too many attempts: “Too many attempts. Please wait 5 minutes before requesting a new code.”
Auto-resend on expiration (with rate limiting) keeps the user in flow without requiring them to find and tap a resend button.
OTP Length and Format
The number of digits in your OTP directly impacts both security and usability.
4-Digit vs 6-Digit vs 8-Digit: When to Use Each
| Length | Combinations | Best For | Security Level |
|---|---|---|---|
| 4-digit | 10,000 | Low-risk actions (newsletter signup, non-financial app login) | Standard |
| 6-digit | 1,000,000 | Standard authentication (banking login, payment confirmation) | Strong |
| 8-digit | 100,000,000 | High-security operations (large financial transfers, admin access) | Maximum |
Six digits is the industry standard for good reason. It gives you one million possible combinations — enough to make brute-force attacks impractical within a short expiration window — without overwhelming the user.
Numeric vs Alphanumeric
Stick with numeric-only OTPs for SMS delivery. Here is why:
- Numeric keypads are faster — Mobile devices show the numeric keyboard automatically for digit-only inputs
- No ambiguity — “O” vs “0” and “l” vs “1” cause real errors with alphanumeric codes
- SMS autofill works reliably — Platform autofill APIs (Android, iOS) are optimized for numeric codes
- Accessibility — Screen readers handle numeric sequences more predictably
Reserve alphanumeric codes for email-based verification where users can copy-paste, and the additional entropy justifies the UX cost.
Accessibility Considerations
Implement autocomplete="one-time-code" on your input fields. This single attribute unlocks:
- iOS/Safari auto-fill from SMS
- Android autofill framework integration
- Password manager OTP capture
For screen reader users, use aria-label="Enter 6-digit verification code" and ensure the input accepts the full code in a single field — splitting across six separate inputs creates a navigation challenge for assistive technology.
Rate Limiting Strategies
Without rate limiting, a 6-digit OTP gives an attacker one million guesses. With rate limiting, they get five. Build your limits in layers.
Per-Phone-Number Limits
Limit OTP sends by the recipient phone number — not just by user account. This prevents attackers from burning through your SMS budget by requesting codes to arbitrary numbers.
Recommended limits:
- OTP sends: 5 per phone number per hour
- Verification attempts: 3 per code, then require a new code
- Daily cap: 10 OTPs per phone number per 24 hours
Per-IP Limits for Bot Detection
Layer IP-based limits on top of phone-number limits to catch automated attacks:
# Python / Flask rate limiting middleware
from flask_limiter import Limiter
from flask_limiter.util import get_remote_address
limiter = Limiter(
app,
key_func=get_remote_address,
default_limits=["200 per day", "50 per hour"]
)
@app.route("/api/otp/send", methods=["POST"])
@limiter.limit("5 per minute")
def send_otp():
phone = request.json.get("phone")
# Check per-phone limit in Redis
phone_key = f"otp_send:{phone}"
count = redis.incr(phone_key)
if count == 1:
redis.expire(phone_key, 3600) # 1-hour window
if count > 5:
return jsonify({"error": "Too many requests"}), 429
# Generate and send OTP
return send_otp_to_phone(phone)
Progressive Delays (Exponential Backoff)
Rather than hard-blocking after a limit is hit, progressively slow down requests:
| Failed Attempt | Delay Before Next Attempt |
|---|---|
| 1st | No delay |
| 2nd | 30 seconds |
| 3rd | 1 minute |
| 4th | 5 minutes |
| 5th+ | 15 minutes (or require alternative verification) |
This approach frustrates automated attacks while giving legitimate users who mistype a reasonable retry experience.
Node.js Rate Limiting Example
// Express middleware with rate-limiter-flexible
const { RateLimiterRedis } = require('rate-limiter-flexible');
const Redis = require('ioredis');
const redisClient = new Redis({ host: 'localhost', port: 6379 });
const otpSendLimiter = new RateLimiterRedis({
storeClient: redisClient,
keyPrefix: 'otp_send',
points: 5, // 5 OTP sends allowed
duration: 3600, // per 1 hour
});
const otpVerifyLimiter = new RateLimiterRedis({
storeClient: redisClient,
keyPrefix: 'otp_verify',
points: 3, // 3 verification attempts
duration: 300, // per 5 minutes
});
async function otpSendMiddleware(req, res, next) {
try {
await otpSendLimiter.consume(req.body.phone);
next();
} catch (rateLimiterRes) {
const retryAfter = Math.ceil(rateLimiterRes.msBeforeNext / 1000);
res.set('Retry-After', retryAfter);
res.status(429).json({
error: 'Too many OTP requests',
retry_after_seconds: retryAfter
});
}
}
OTP Delivery Channel Selection
The channel you deliver OTPs through affects security, reach, and cost. Choose based on your audience and risk profile.
SMS vs Voice vs Email: Decision Matrix
| Factor | SMS | Voice Call | |
|---|---|---|---|
| Delivery speed | 2-5 seconds | 15-30 seconds | 10-60 seconds |
| Reach (Africa) | Highest — works on every phone | High — works on feature phones | Lower — requires data/Wi-Fi |
| User effort | Low (autofill capable) | Medium (listen + type) | Medium (switch apps) |
| Security | Moderate (SIM swap risk) | Moderate (voicemail interception) | Lower (email compromise risk) |
| Accessibility | Good | Excellent (hearing impaired excluded) | Good |
| Cost | Low per message | Higher per call | Lowest |
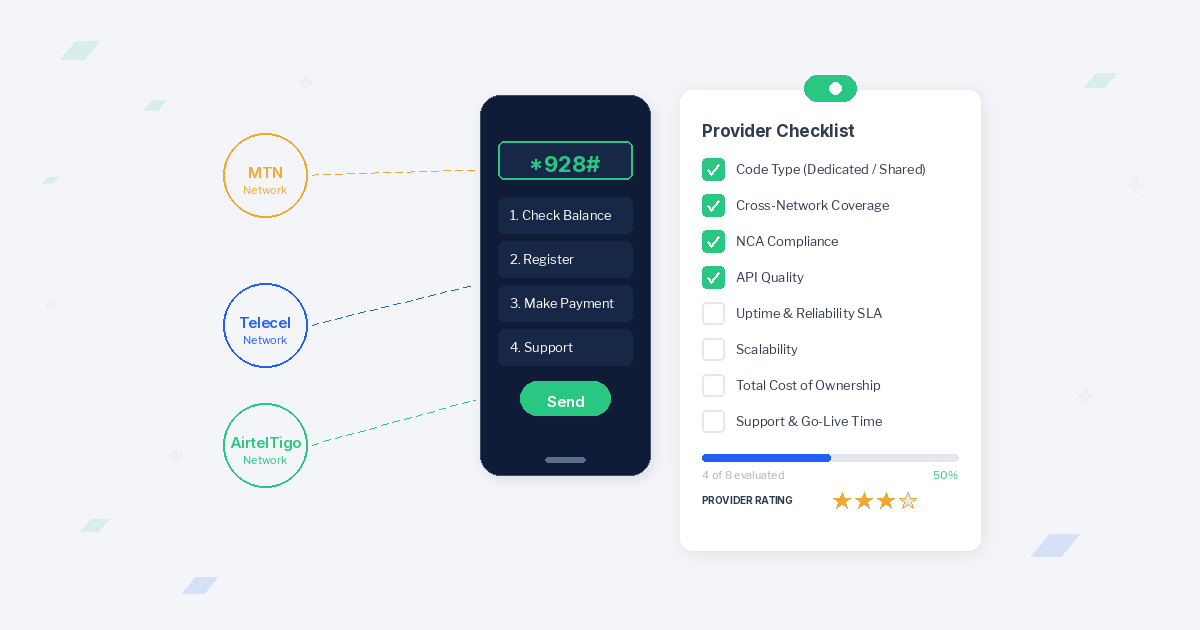
For African markets, SMS remains the dominant OTP channel. It works on every phone — feature phones and smartphones alike — and doesn’t require a data connection. With direct carrier connections (MTN, Vodafone, AirtelTigo), delivery is fast and reliable even in areas with limited internet infrastructure.
When deciding between SMS and voice for business communication, the answer for OTP delivery is almost always SMS-first with voice as a fallback.
Build Fallback Chains
Don’t rely on a single channel. Implement automatic fallback when the primary channel fails:
- SMS (primary) — Fastest, most reliable for mobile users
- Voice call (fallback after 60 seconds) — Catches users who can’t receive SMS
- Email (fallback after voice fails) — Last resort for users with connectivity issues
Trigger the fallback automatically. Don’t make the user hunt for a “try voice call instead” link — surface it prominently with a clear timer showing when the next option becomes available.
Multi-Channel for Critical Transactions
For high-value operations (large transfers, account deletion), consider requiring confirmation across two channels simultaneously — SMS code plus email confirmation. This makes SIM swap attacks insufficient on their own.
Arkesel’s SMS Platform delivers OTPs with direct mobile network connections across Ghana and Africa, giving you the reliability that mission-critical authentication demands. Pair it with VoiceConnect for voice-based fallbacks.
UX Best Practices for OTP Input
The best security architecture fails if users can’t complete the verification flow. OTP UX directly impacts completion rates.
Auto-Fill Support
Implement the WebOTP API for browser-based auto-fill. Here is the minimal setup:
<!-- HTML input with autocomplete hint -->
<input
type="text"
inputmode="numeric"
pattern="[0-9]{6}"
autocomplete="one-time-code"
maxlength="6"
aria-label="Enter 6-digit verification code"
/>
// WebOTP API (Chrome on Android)
if ('OTPCredential' in window) {
const ac = new AbortController();
setTimeout(() => ac.abort(), 5 * 60 * 1000); // 5-min timeout
navigator.credentials.get({
otp: { transport: ['sms'] },
signal: ac.signal
}).then(otp => {
document.getElementById('otp-input').value = otp.code;
document.getElementById('otp-form').submit();
});
}
For domain-bound OTP messages (required by the WebOTP API), format your SMS as:
Your verification code is 847293.
@arkesel.com #847293
The last line tells the device which domain the code belongs to, preventing phishing sites from intercepting auto-fill.
Timer Displays and Input Fields
Show a visible countdown timer next to the input field. Users who see “Code expires in 2:34” are less likely to panic-rush and mistype.
Design rules:
- Single input field — Don’t split into six boxes. A single field with
inputmode="numeric"supports paste, autofill, and assistive technology - Large, centered text — OTP digits should be visually prominent, not buried in a form
- Auto-advance to next step — Submit automatically when all digits are entered
- Clear the field on error — Don’t make users manually delete wrong digits
Resend Flow Design
The resend button is the safety net. Design it to reduce both user frustration and abuse:
- Disable the resend button for 30-60 seconds after sending (show countdown)
- After the first resend, increase the cooldown to 2 minutes
- After 3 resends, offer voice call as an alternative
- After 5 total attempts, require the user to restart the flow
Error Messaging That Doesn’t Leak Information
Your error messages should guide users without giving attackers intelligence:
- Do: “That code doesn’t match. Please try again.”
- Don’t: “That code was already used.” (Confirms a valid code existed)
- Don’t: “No OTP found for this number.” (Confirms the number isn’t in your system)
- Don’t: “OTP expired 3 minutes ago.” (Reveals your expiration window)
Keep error messages helpful but generic. The less an attacker learns from failure, the better.
OTP Security Best Practices
The OTP itself is only as secure as the systems storing, transmitting, and validating it.
With NIST SP 800-63B-4 classifying SMS OTP as a “restricted authenticator,” the implementation details matter more than ever. The classification doesn’t mean SMS OTP is obsolete — it means you need to compensate for the channel’s known weaknesses with stronger server-side controls. Every practice below directly addresses the risks that earned SMS its restricted status.
Hash OTPs in Storage
Never store plaintext OTPs in your database. If your database is compromised, every active OTP is exposed.
# Python: Store hashed OTP with expiration
import hashlib
import secrets
import time
def generate_otp(length=6):
otp = ''.join([str(secrets.randbelow(10)) for _ in range(length)])
otp_hash = hashlib.sha256(otp.encode()).hexdigest()
return otp, otp_hash
def store_otp(redis_client, phone, otp_hash, ttl=300):
key = f"otp:{phone}"
redis_client.setex(key, ttl, otp_hash)
def verify_otp(redis_client, phone, user_input):
key = f"otp:{phone}"
stored_hash = redis_client.get(key)
if not stored_hash:
return False
input_hash = hashlib.sha256(user_input.encode()).hexdigest()
if input_hash == stored_hash.decode():
redis_client.delete(key) # One-time use
return True
return False
Use SHA-256 for OTPs (not bcrypt). OTPs are short-lived and low-entropy — the computational cost of bcrypt isn’t necessary, and hashing speed matters for verification UX.
Enforce One-Time Use
Delete or invalidate the OTP immediately after successful verification. This sounds obvious, but implementation gaps are common:
- Delete the OTP record from your store (Redis, database) on successful verification
- If using a database, set a
used_attimestamp and check it before validation - Handle race conditions — use atomic operations (Redis
GETDEL, database transactions) to prevent a single OTP from being verified twice in parallel requests
Bind OTP to Specific Action
An OTP generated for login should not work for a password reset. Bind each OTP to its intended action:
# Store OTP with action context
def store_otp(redis_client, phone, otp_hash, action, ttl=300):
key = f"otp:{action}:{phone}"
redis_client.setex(key, ttl, otp_hash)
# Verify only matches the intended action
def verify_otp(redis_client, phone, user_input, action):
key = f"otp:{action}:{phone}"
stored_hash = redis_client.get(key)
# ... verification logic
This prevents an attacker who intercepts a low-risk OTP (newsletter signup) from using it for a high-risk action (fund transfer).
Brute-Force Protection Layers
Combine multiple defenses:
- Attempt limits: Lock the OTP after 3 failed verification attempts
- Account-level throttling: Flag accounts with repeated OTP failures for review
- CAPTCHA escalation: Require CAPTCHA after 2 failed attempts before allowing another OTP request
- Anomaly detection: Monitor for patterns — rapid requests from new IPs, requests to sequential phone numbers, or verification attempts from different IPs than the OTP request
Putting It All Together: Implementation Checklist
Before launching your OTP system to production, verify each of these:
| Category | Requirement | Status |
|---|---|---|
| Expiration | Risk-appropriate expiration windows configured per use case | |
| Expiration | Clear error messages distinguishing expired vs invalid codes | |
| Format | 6-digit numeric codes for SMS delivery | |
| Rate Limiting | Per-phone, per-IP, and per-account limits in place | |
| Rate Limiting | Exponential backoff on failed attempts | |
| Delivery | Fallback chain configured (SMS → Voice → Email) | |
| UX | autocomplete="one-time-code" on input fields | |
| UX | Countdown timer visible to user | |
| UX | Resend flow with progressive cooldowns | |
| Security | OTPs hashed in storage (never plaintext) | |
| Security | One-time use enforced with atomic operations | |
| Security | OTPs bound to specific action context |
Frequently Asked Questions
What is the recommended OTP expiration time?
It depends on the use case. For login OTPs, 30-60 seconds strikes the right balance between security and usability. Transaction confirmations work well at 3-5 minutes. Account recovery OTPs can extend to 10-15 minutes. NIST recommends no longer than 10 minutes for any OTP type.
How many OTP attempts should I allow before locking?
Allow 3 verification attempts per OTP code. After 3 failures, invalidate the code and require the user to request a new one. For OTP sends, limit to 5 per phone number per hour and 10 per day. This stops brute-force attacks while accommodating legitimate typos.
Should I use 4-digit or 6-digit OTPs?
Use 6-digit OTPs for any authentication or financial operation. A 4-digit code has only 10,000 possible combinations — vulnerable to brute force without aggressive rate limiting. Six digits give you 1,000,000 combinations, which is enough to make brute force impractical within a standard expiration window.
How do I prevent OTP SMS pumping attacks?
OTP SMS pumping is a fraud scheme where attackers trigger massive volumes of OTP messages to premium-rate numbers. Defend against it with per-phone rate limits, geographic filtering (block sends to unexpected countries), phone number verification before sending, and real-time cost anomaly monitoring. For a deep dive, read our guide on OTP SMS pumping and fraud prevention.
Is SMS OTP still secure in 2026?
SMS OTP is not the strongest authentication factor — SIM swap attacks and SS7 vulnerabilities are real risks. NIST SP 800-63B-4 classifies it as a “restricted authenticator,” acknowledging these weaknesses while confirming it remains acceptable with proper safeguards. For most applications, SMS OTP with proper rate limiting, short expiration windows, and hashed storage remains a practical and effective solution. It works on every phone, requires no app installation, and is familiar to users. For critical systems, layer SMS OTP with additional factors rather than replacing it entirely.
Build Secure OTP Flows With the Right Infrastructure
Implementation best practices only matter when your delivery infrastructure is reliable. A perfectly configured OTP system fails if messages arrive late or not at all.
Arkesel’s SMS Platform delivers OTPs through direct mobile network connections across Africa — MTN, Vodafone, AirtelTigo — with a 99.9% delivery rate and real-time delivery tracking. Pair it with the OTP API integration guide to build authentication flows that are fast, secure, and developer-friendly.
Start building with Arkesel and implement OTP best practices on infrastructure your users can trust.
Explore the OTP Developer Guide Series
- OTP API Integration Guide: Architecture, Code Examples & Testing (Pillar)
- OTP API Setup Tutorial: Complete Integration Guide
- OTP API Errors: 10 Common Issues and How to Fix Them
- 7 Reasons to Use a Plug-and-Play OTP API for Instant Verification
- OTP Security: 5 Ways to Strengthen Digital Safety
- OTP SMS Pumping and Fraud Prevention
- Best OTP API Providers Compared: Twilio vs Vonage vs Arkesel (2026)
Related Articles
- OTP API Integration Guide: Architecture, Code Examples & Testing
- OTP SMS Pumping and Fraud Prevention
- Best OTP API Providers Compared: Twilio vs Vonage vs Arkesel (2026)
- OTP for Fintech Banking: Secure Transactions at Scale
- SMS OTP vs Authenticator App vs Email OTP: Choosing the Right Delivery Channel
- How Do OTPs Work? The 2026 Guide for African Fintech