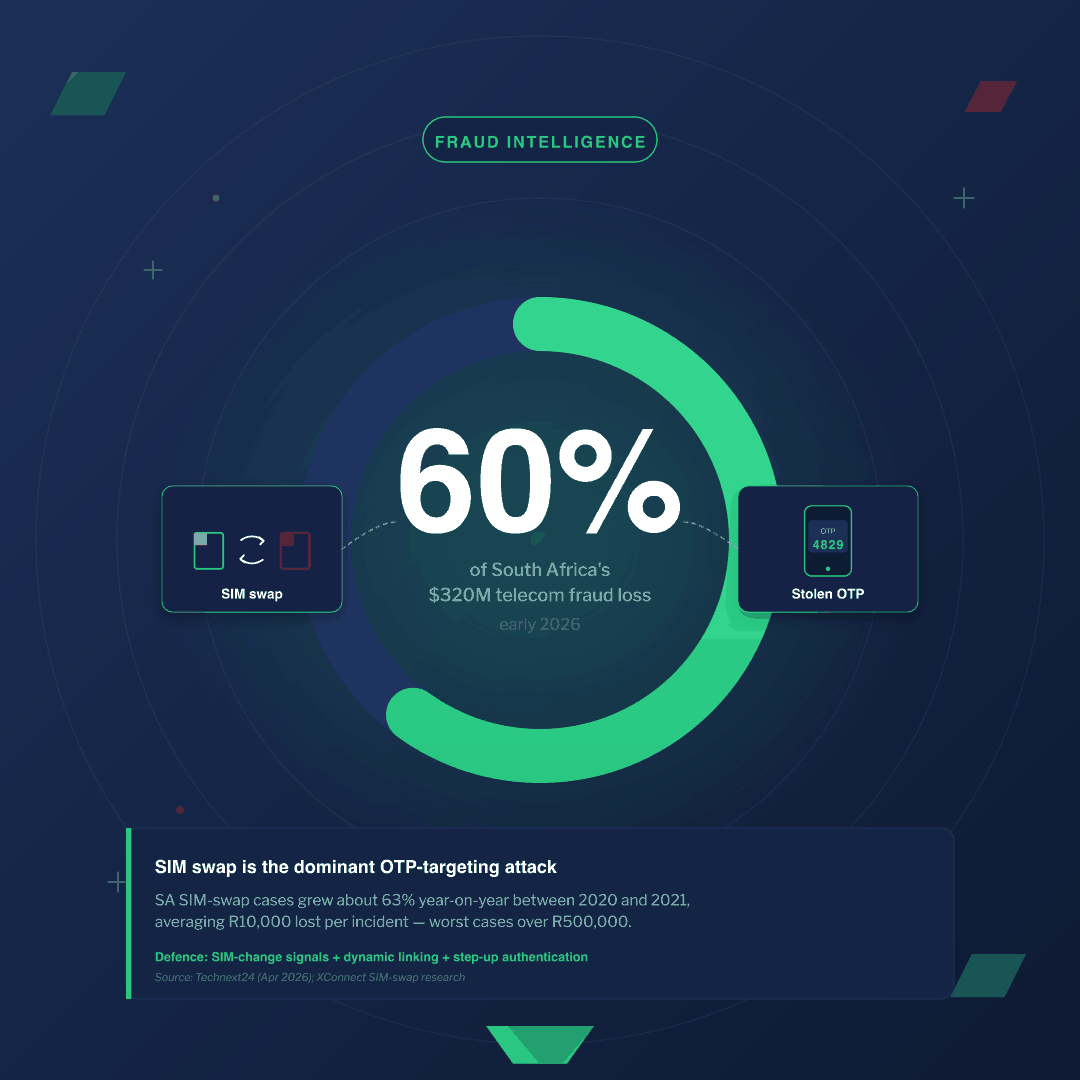
OTP for fintech banking is the layered authentication rail that ties every transaction to a verified user, a verified device, and a verified amount — not a single SMS code in isolation. African fraud teams already live with one uncomfortable truth: SIM swaps alone accounted for roughly 60% of South Africa’s $320 million telecom fraud loss reported in early 2026, and every one of those swaps was, at its core, an attack on an OTP. (Source: Technext24, April 2026)
Yet OTP is not the problem. The problem is OTP architected as a single, naked SMS code instead of as one layer in a regulator-aligned, risk-scored, dynamically-linked defence. This guide shows you how to architect OTP for fintech banking properly — for banks, mobile-money operators, payment processors, and digital lenders across Africa — and how to scale it from your first ten transactions a day to a million.
How banks and fintech apps use OTPs
Banks and fintechs use OTPs as a possession factor inside multi-factor authentication — never the only check. A one-time password is a short, single-use code that proves the user holds something — a SIM, an authenticator app, or a registered device — at the exact moment they act.
Real banking and fintech systems use OTPs at every moment a wrong actor could cause harm:
- Account login when the device is new, geo-anomalous, or hasn’t been seen in 30 days.
- Transaction authorisation for transfers, bill payments, airtime top-ups, and mobile-money cash-outs.
- Beneficiary add and beneficiary edit — the highest-risk fraud surface, since a fraudulent payee turns into every future transaction.
- Profile changes — phone number, email, biometric enrolment, PIN reset.
- KYC and onboarding to confirm the applicant controls the phone number on the application.
- Card-not-present payments via 3-D Secure 2 challenges.
- Mobile-money cash-out at the agent counter, before money leaves the wallet.
Microsoft research found that multi-factor authentication blocks more than 99.9% of automated account-compromise attacks — a figure Microsoft continues to cite as canonical guidance through 2026. (Source: Microsoft Security Blog, 2019) OTP is how most African fintechs make that math real on a feature phone, a basic Android, and a flagship — all at the same time.
The fintech-OTP regulatory landscape
If you operate in Africa, three regulatory regimes already shape your OTP design — even if you’ve never read them end-to-end.
Nigeria — CBN Risk-Based Cybersecurity Framework
The Central Bank of Nigeria issued the Risk-Based Cybersecurity Framework and Guidelines for Deposit Money Banks and Payment Service Banks on 31 May 2024, with an effective date of 1 July 2024. Supervised financial institutions must report cyber incidents within 24 hours and apply risk-based controls to authentication and payment systems. (Source: CBN, May 2024)
In practice, that means three things for your OTP stack: tier authentication strength by transaction risk, log every authentication decision in a way you can hand to a regulator, and have an incident playbook that gets a SIM-swap or AIT attack into a CBN report within 24 hours.
Ghana — Bank of Ghana CISD
The Bank of Ghana issued an exposure draft of a revised Cyber and Information Security Directive in September 2025 and is rolling out a 2026 directive covering banks, specialised deposit-taking institutions, payment systems, and fintech companies. The framework mandates strong authentication, encryption of biometric data in transit, and a 20-section compliance regime. (Source: Bank of Ghana, September 2025)
For an OTP architect, the BoG CISD reads as a clear instruction: assume strong customer authentication is the floor, not the ceiling, and treat your delivery channel as a regulated control — not just a vendor choice.
Europe — PSD2 and the dynamic linking standard
Even if you don’t process euros, PSD2 matters. It sets the global blueprint regulators in Africa quietly align to.
PSD2 Strong Customer Authentication requires multi-factor authentication using at least two of three factors — knowledge, possession, or inherence. For electronic payments it additionally requires dynamic linking, tying the authentication code to the specific transaction amount and recipient. Traditional standalone SMS OTPs cannot meet dynamic linking on their own. (Source: PSD2 RTS on SCA)
The takeaway is operational: the OTP message itself must carry the amount and recipient, and the back-end must reject any code whose payload no longer matches the pending transaction. We come back to dynamic linking in the architecture section below.
The fintech threat model — what an attacker actually does to defeat OTP
Designing OTP without a threat model is theatre. Africa-focused fraud teams should plan for six attack patterns:
- SIM swap. A fraudster social-engineers the MNO or a corrupt agent into porting the victim’s number to a new SIM. Every OTP after that lands on the attacker’s phone.
- SIM cloning of older SIM profiles, less common but still seen in markets with legacy SIM stock.
- SMS pumping and Artificially Inflated Traffic (AIT). A premium-route operator triggers your OTP API thousands of times to harvest interconnect revenue — a cost-side attack that quietly bankrolls fraud rings. See how to defend OTP against SMS pumping.
- Phishing relay — the victim types the OTP into a fake bank page; the attacker forwards it to the real bank in real time. Modern adversary-in-the-middle kits make this a one-click attack.
- Trojan SMS interception on rooted or sideloaded Android phones, where a malicious app reads the OTP before the user does.
- Social engineering — call-centre staff convinced to read OTPs over the phone, or customers convinced to share them.
Identity theft accounts for an estimated 63% of all digital financial crime in Africa, costing approximately $4 billion annually. (Source: XConnect, 2024) The same XConnect report shows SIM swap cases in South Africa grew roughly 63% year-on-year between 2020 and 2021 — from 2,686 to 4,386 reported incidents — and continued to climb around 25% year-on-year afterward, with an average loss per incident around R10,000 and worst cases exceeding R500,000.
This is not just a regional pattern. The FBI’s Internet Crime Complaint Center recorded 982 SIM swap complaints and $25,983,946 in reported losses in 2024, averaging more than $26,400 per victim. (Source: Deepstrike analysis of FBI IC3 data) Treat SIM swap as the dominant OTP-targeting attack worldwide. Architect for it.
For the deeper attack-side checklist, see Arkesel’s five ways to strengthen OTP security.
OTP delivery channels for financial services
No single channel wins every fintech use case. Pick channels by transaction risk and customer device reality.
| Channel | Security | Accessibility | Regulatory acceptance | Best fit |
|---|---|---|---|---|
| SMS | Medium (SIM-swap, AIT exposed) | Universal — works on every phone | Accepted as one SCA factor; needs dynamic linking for payments | Default for African mobile-money and feature-phone banking |
| Voice (IVR/TTS) | Medium | Universal; reaches no-data users | Accepted; useful for accessibility | Fallback when SMS fails; users in low-signal zones |
| USSD | Medium-high (session-bound, network-controlled) | Universal on GSM | Accepted; common for mobile-money cash-out | High-risk transactions on feature phones; agent banking |
| Authenticator app (TOTP) | High | Smartphone only | Strong SCA possession factor | Internal staff, premium retail tier, SME banking dashboards |
| Push (signed in-app) | High | App users only | Strong SCA possession factor; supports dynamic linking | Primary banking app users |
| Low | Universal but slow | Weak factor; not advised for payments | Account-recovery only, never transaction authorisation |
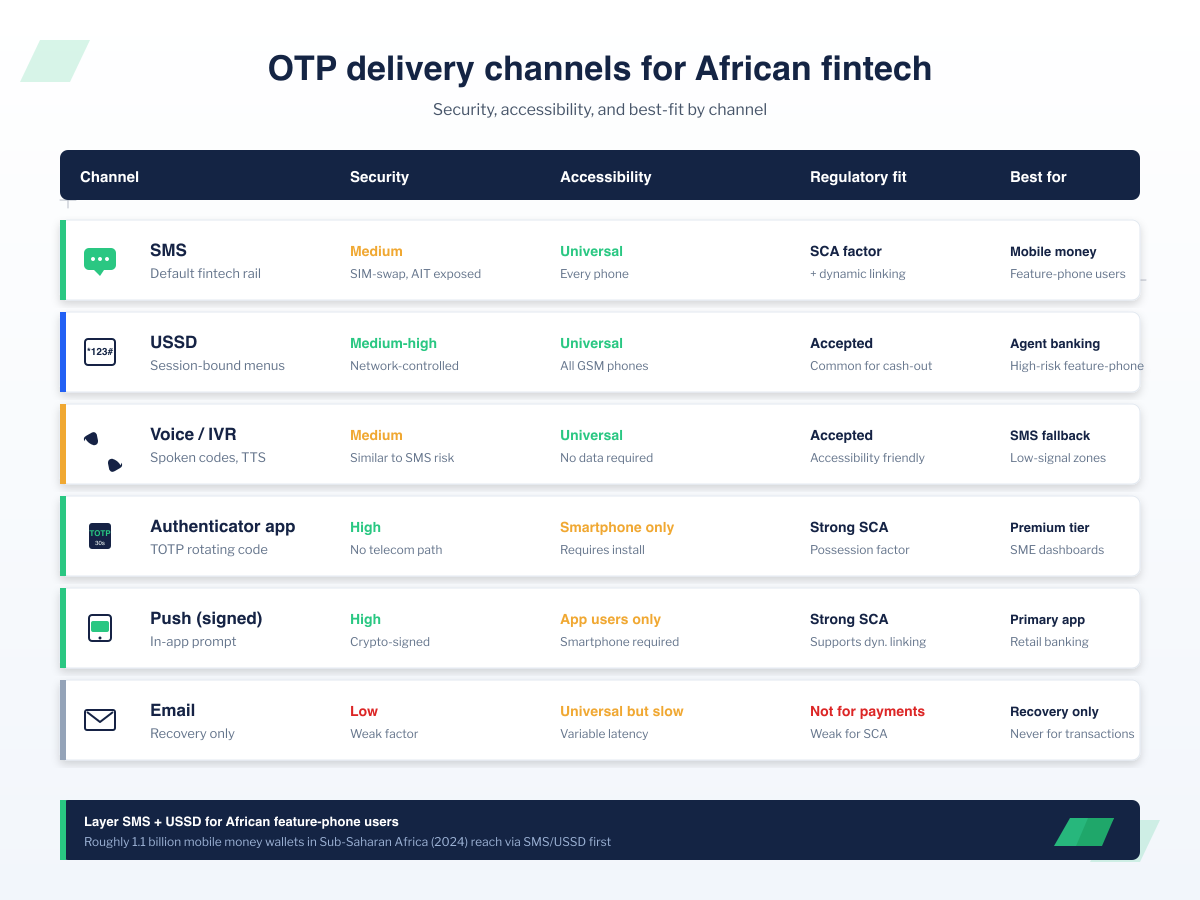
SMS OTP dominates African fintech for a reason. In 2024, registered mobile money wallets in Sub-Saharan Africa grew at double-digit rates, reaching approximately 1.1 billion accounts. (Source: Fintech News Africa, 2024) The phones underneath those wallets are mostly basic Android and feature phones. SMS — and increasingly USSD — is the only OTP rail that reaches every customer the regulator counts. The right move is to layer SMS, not replace it.
See how USSD financial services in Africa extend OTP and step-up flows to feature-phone users.
See how Arkesel’s OTP and USSD rails power transaction authentication for African banks, mobile-money operators, and digital lenders. Talk to our enterprise team.
OTP transaction security architecture for fintech
A modern OTP for fintech banking stack is not a single function. It is a six-layer pipeline that runs on every sensitive action.
1. Risk scoring. Score every transaction before you decide how to authenticate. Inputs: device fingerprint, behavioural biometrics, geo-velocity, time of day, beneficiary novelty, amount versus user baseline, channel. Output: a risk band — low, medium, high.
2. Channel choice. Low-risk transactions get silent verification — the user already approved on the device. Medium-risk transactions get a standard SMS or push OTP. High-risk transactions get step-up — a fresh OTP plus an additional possession or inherence factor.
3. Dynamic linking. Every OTP message for a payment must carry the amount and recipient inside the SMS body. Your back-end must reject any code whose pending transaction details no longer match. This is the PSD2 rule, and it’s the cheapest defence against phishing-relay attacks.
4. SIM-swap signal integration. Before sending the OTP, query the MNO or an MNO-aggregator signal for recent SIM change events on that MSISDN. If the SIM swapped in the last 24–72 hours, block the high-risk action and force an out-of-band re-verification.
5. SMS-pumping and AIT defence on the send side. Rate-limit OTP issuance per number, per IP, per device, and per route. Detect cost anomalies on premium destinations. Drop traffic to known AIT-implicated number ranges. The OTP expiration and rate limiting best practices post covers this in implementation depth.
6. Audit logging for regulatory traceability. Every OTP issuance, every validation outcome, every step-up decision must land in an immutable log with timestamp, channel, risk score, and decision rationale. CBN and BoG both expect you to produce this on request.
For the broader build pattern, the cluster pillar covers it end to end: OTP API integration guide.
Implementation playbook — what to build first
If you’re standing up OTP for a new fintech, or hardening an existing stack, ship in this order:
- Set OTP length, expiry, and lockouts. Six digits, 60–120 second expiry, three attempts then lock, sliding-window rate limit per MSISDN. See the OTP API setup tutorial.
- Add risk scoring. Even a simple device-plus-geo-plus-amount score outperforms uniform OTP everywhere.
- Wire dynamic linking into the SMS template and the verification call. This is the regulatory unlock.
- Add SIM-swap signals. Start with MNO-aggregator APIs in your three largest markets.
- Harden against SMS pumping. Per-route caps, premium-destination blocks, anomaly alerts.
- Build the BCP. Define what happens when your primary SMS route degrades — failover to voice, to USSD, to push, and the regulator-visible logs that prove you did so. Compare your options in the OTP API providers comparison.
- Ship the audit log. Immutable, queryable, retention-aligned to CBN and BoG requirements.
If you hit integration friction along the way, the common OTP API integration errors post is the fastest unblock.
The scale problem — why OTP architecture is a fintech-survival question
The transaction volumes African fintechs already serve make this work non-negotiable.
M-PESA processed 28 billion transactions worth KES 40 trillion — approximately $309 billion — across the Safaricom group in FY2023/24, and reached 40 million active customers in Kenya as of March 2026. (Source: Safaricom FY25 Earnings Booklet, May 2025) MTN MoMo serves 69.1 million active users across 16 African countries and processed 338 million financial transactions via MoMo APIs in 2022. (Source: Ericsson / MTN MoMo Open APIs case study, 2023)
At that scale, your OTP system is not a feature. It is the trust rail your entire business sits on. A 0.1% delivery dip or a 30-second latency spike compounds into measurable customer attrition the same week.
How Arkesel powers OTP for African fintech
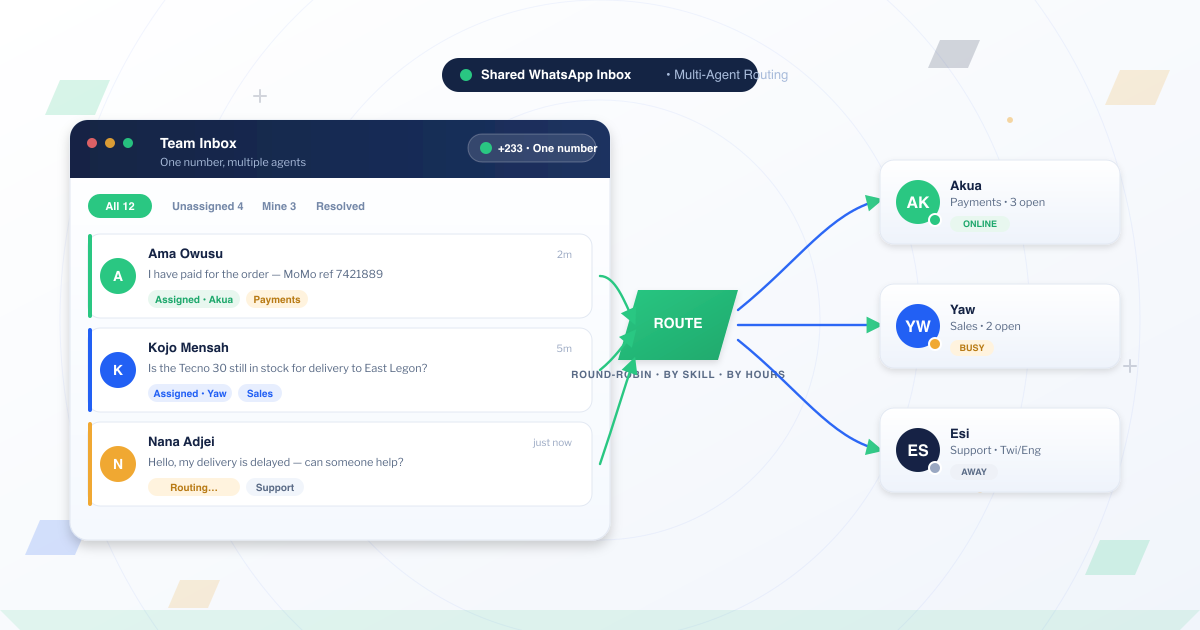
Arkesel is the OTP for fintech banking infrastructure layer built for African financial services. Three things matter:
- Direct MNO connections across Ghana, Nigeria, and South Africa — fewer hops, faster delivery, lower SMS-pumping exposure.
- AIT and SMS-pumping defences built into the Arkesel SMS Platform and phone number verification products — so the cost-side attack pattern doesn’t quietly drain your fraud budget.
- USSD as a first-class fallback via Arkesel USSD — so a feature-phone customer in a low-coverage area still completes the cash-out.
- 99.9% delivery SLA with real-time delivery tracking, ISO 27001 certified.
Developers can ship against the Arkesel developer APIs in an afternoon. The plug-and-play OTP API covers the standard verification flow with rate limits, expiry, and audit logging out of the box. For current pricing, see Arkesel pricing.
Frequently asked questions about OTP for fintech and banking
How do banks and fintech apps use OTPs?
Banks and fintechs use OTPs as a possession factor inside multi-factor authentication — at login from new devices, on transaction authorisation, when adding or editing a beneficiary, on profile changes, during KYC, on card-not-present 3-D Secure flows, and at mobile-money cash-out.
Is SMS OTP secure enough for mobile banking in Africa?
SMS OTP is secure enough when it is one layer in a risk-scored, dynamically-linked stack with SIM-swap signals and SMS-pumping defence — not when it is the only check. For a feature-phone customer base, layered SMS plus USSD remains the only realistic option.
Does PSD2 allow SMS OTP for payments?
PSD2 permits SMS OTP as the possession factor inside Strong Customer Authentication, but for electronic payments it additionally requires dynamic linking — the code must be tied to the specific amount and recipient. A standalone SMS OTP without dynamic linking does not meet the standard.
Does Nigeria’s CBN cybersecurity framework allow SMS OTP?
The CBN Risk-Based Cybersecurity Framework requires authentication controls to be proportional to transaction risk and mandates 24-hour incident reporting. SMS OTP remains acceptable as one factor inside a layered, risk-scored architecture, with logging and incident response that meet the framework’s reporting and traceability expectations.
How do banks prevent SIM-swap fraud on OTP?
The defensible pattern is: query an MNO SIM-change signal before sending an OTP for a high-risk action, block the OTP if a recent swap is detected, and force out-of-band re-verification — paired with risk scoring, dynamic linking, and step-up authentication.
What is dynamic linking in transaction authentication?
Dynamic linking is the requirement that an authentication code is mathematically tied to the specific amount and recipient of a payment. If the amount or recipient changes after the code is issued, the code becomes invalid — which defeats phishing-relay attacks that swap the payee mid-flow.
Related Articles
- SMS OTP vs Authenticator App vs Email OTP: Choosing the Right Delivery Channel
- How Do OTPs Work? The 2026 Guide for African Fintech
Conclusion
OTP is not dead. OTP done as a single SMS code, with no risk scoring, no dynamic linking, and no SIM-swap signals — that is dead. The fintech that wins the next five years in Africa is the one that builds the layered version on rails that actually reach every customer.
Build that stack on infrastructure designed for African networks, African regulators, and African transaction volumes.
Build production-grade fintech OTP on Arkesel — direct MNO routing across Africa, SIM-swap and SMS-pumping defences built in. Create a free Arkesel account or talk to our enterprise team.