There is no universal winner in the SMS OTP vs authenticator app debate. The right channel depends on the risk tier of the action, the device your user actually owns, and where they are when they try to log in.
This guide breaks down every major OTP delivery channel honestly — strengths, weaknesses, and the African deployments where each one shines. By the end, you will have a decision matrix you can ship.
The Five OTP Delivery Channels at a Glance
Most teams treat OTP as a single channel decision. It is not. You have five practical options: SMS, Voice, Email, Authenticator Apps (TOTP), and Push.
Each channel has a different cost shape, attack surface, device requirement, and UX profile. Here is the high-level OTP delivery channel comparison.
| Channel | Speed | Device Requirement | UX Friction | African Deliverability | Best Risk Tier |
|---|---|---|---|---|---|
| SMS | Seconds | Any phone with a SIM | Lowest — universal | Strong via direct carrier routes | Low to medium |
| Voice (IVR) | Seconds to minutes | Any phone | Low — accessible | Strong, works on weak data | Low to medium, accessibility |
| Seconds to minutes | Internet-connected device | Medium — context switch | Strong where email is the primary inbox | Low | |
| Authenticator App (TOTP) | Instant (offline) | Smartphone with app installed | High first-time setup | Excellent once installed | Medium to high |
| Push | Instant | Smartphone with your app installed | Lowest — single tap | Strong on Wi-Fi or 4G | Medium to high |
Now let us break each one down.
SMS OTP — How It Works and Where It Wins
A six-digit code is generated on your server and delivered via the mobile carrier’s SMS channel. The user reads the code and types it back into your app.
Strengths:
- Universal device reach — every phone with a SIM card can receive it, smartphone or feature phone.
- Zero app install at signup. The friction-free default for first-time mobile users.
- Mobile money users already trust the SMS confirmation pattern. It feels native.
- Effective security in practice. Google’s data shows two-step verification via SMS can stop 100% of automated attacks, 96% of bulk phishing attacks, and three-quarters of targeted attacks.
Weaknesses:
- SIM-swap fraud is real for high-value accounts where the attacker can compromise a SIM directly.
- SS7 interception is a known attack vector at the carrier-protocol layer.
- SMS pumping fraud — bots inflating traffic on premium routes — is an operational cost risk if your stack is not configured to detect it. Our guide to preventing SMS pumping fraud covers the controls that close this gap.
When to use SMS: Mobile money confirmation, retail banking login, e-commerce checkout, and any flow where universal device reach matters more than the marginal security gain of TOTP.
Deliverability is also a function of routing. SMS sent through direct carrier connections — like the Arkesel SMS Platform routes to MTN, Vodafone, and AirtelTigo — lands faster and more reliably than SMS routed through aggregated international gateways. That single architectural choice is often the difference between a 60-second OTP and a failed verification.
Voice OTP — The Channel Most Teams Underrate
A voice call is placed to the user’s phone and an IVR reads out the code, often in their local language.
Strengths:
- Works on the weakest data connection — voice carrier signal is more resilient than mobile data in rural areas.
- Ideal for low-literacy users and visually impaired users who struggle with SMS text.
- Multi-language IVR lets you serve Twi, Ga, Hausa, Yoruba, French, and English from a single OTP flow.
Weaknesses:
- Slower than SMS — the user has to pick up.
- Carrier-call latency varies by route.
- More expensive per verification than SMS.
When to use Voice: Accessibility fallback when SMS fails, low-literacy user segments, and high-value transactions where you want the friction of an extra confirmation step. VoiceConnect delivers crystal-clear IVR across African networks for exactly this use case.
Email OTP vs SMS OTP — Where Email Is the Right Default
A code is emailed to the user’s verified address. They open the email, copy the code, and paste it into your app.
Strengths:
- Free at scale. No per-message carrier cost.
- Works internationally with no SIM or roaming concerns.
- Room for context — you can include the IP address, device, and a clear reason for the OTP in the message body.
Weaknesses:
- Slower delivery. Some users wait minutes for the message to land.
- Spam folder risk reduces deliverability.
- Requires the user to context-switch to their email client mid-flow.
When to use Email: Low-risk web flows where the user is already signed into their email — newsletter signup verification, B2B SaaS account confirmation, password reset on a desktop session. Email OTP is a primary channel for these cases, not just a fallback.
Authenticator Apps (TOTP) vs SMS 2FA — When the Smartphone Is Already In Hand
The user installs Google Authenticator, Authy, or a similar app, scans a QR code once, and the app generates a fresh six-digit code every 30 to 60 seconds. Codes are generated locally on the device using a shared secret and the current time, with no network round-trip.
Strengths:
- Resistant to SIM swap and SS7 interception — there is no SMS in the chain to attack.
- Operates entirely offline. The user does not need network connectivity to generate a code.
- Low marginal cost per verification once the user is set up.
Weaknesses:
- Requires a smartphone. This excludes feature-phone users entirely.
- Requires the user to install an app, scan a QR code, and understand the model — a non-trivial friction at first-time setup.
- Account-recovery complexity. If the user loses their device and you have no recovery channel, the account is locked.
When to use TOTP: Medium-to-high risk accounts where the user already has a smartphone — admin consoles, developer dashboards, opt-in upgrade for high-value consumer accounts. Major US security agencies and standards bodies recommend app-based or hardware-based authentication over SMS-based MFA for sensitive accounts, and that guidance applies cleanly when your users own smartphones.
For the security mechanics in depth, our five ways to strengthen OTP security guide covers layered defenses.
Push OTP, Passkeys, and WhatsApp — The Modern Alternatives
Push OTP sends a tap-to-approve prompt directly to your installed mobile app. Passkeys replace OTP entirely with device-bound cryptographic keys. WhatsApp OTP delivers the code through the WhatsApp Business API.
Each has a place. Push is excellent for medium-to-high risk flows where you already have a user with your app installed. Passkeys are the long-term direction for any product with a smartphone-only user base. WhatsApp OTP works well for markets with deep WhatsApp penetration.
The catch — none of these channels yet match SMS for universal device reach in African markets. They are upgrades layered on top of an SMS default, not replacements for it.
The Africa Reality: Why SMS Remains the Dominant OTP Channel
Global security blogs default to one verdict: authenticator apps win. That conclusion ignores the device reality across Sub-Saharan Africa.
Mobile internet access remains uneven across rural Africa. A meaningful share of users in coverage areas are not yet using mobile internet at all, let alone installing niche authenticator apps. The GSMA Handset Affordability Coalition has identified six African countries — DRC, Ethiopia, Nigeria, Rwanda, Tanzania, and Uganda — for 2026 pilots of affordable $30 to $40 4G smartphones, an explicit signal that smartphone affordability is still a multi-year curve.
SMS is the only channel with effectively universal device reach today. Layer on mobile money workflow familiarity, no app install at signup, low data requirements, and direct carrier routes to MTN, Vodafone, and AirtelTigo — and SMS becomes the structurally correct default for most African product teams.
This is also why adoption tells the same story. Research from Exploding Topics 2024 (cited via Notifyre) shows 56% of people use SMS-based 2FA compared to 51% who use email and 31% who use authenticator apps. Even in Western markets where smartphone penetration is near-saturation, SMS still leads.
Decision Matrix: Map Use Case to OTP Channel
Use this matrix to pick the primary and fallback channel for each flow in your product.
| Use Case | Primary Channel | Fallback Channel | Reasoning |
|---|---|---|---|
| Mobile money confirmation | SMS | Voice | Universal device reach, mobile money pattern familiarity |
| Retail banking login | SMS | Voice | Same as above, plus carrier-direct route reliability |
| E-commerce checkout | SMS | Fast, low-friction, no smartphone assumed | |
| Social or SaaS signup | SMS | User is already on email; verify the address they entered | |
| B2B admin and high-value transactions | Authenticator App (TOTP) | SMS | Smartphone assumed for admin users; SMS as recovery channel |
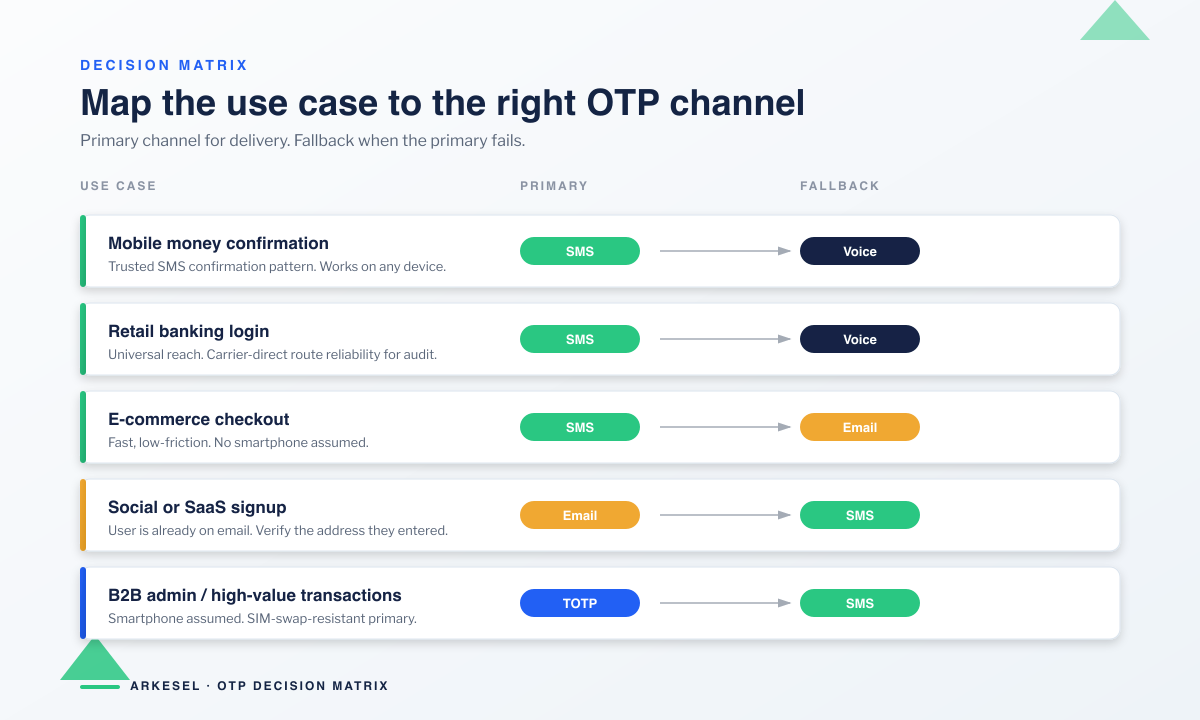
This is not theory — it is how the highest-performing African fintechs already operate. See our breakdown of OTP for fintech and banking transactions for the full pattern.
How to Layer OTP Channels Without Overbuilding
Most African user bases should layer three channels:
- SMS as the universal default — every user can receive it on any phone they already own.
- Authenticator app as an opt-in upgrade — offered to users on high-value accounts who choose stronger protection.
- Email as a low-risk fallback — used for password reset, signup confirmation, and account recovery flows.
Voice sits alongside as the accessibility fallback when SMS fails or the user needs a multi-language IVR experience.
With this layering, you cover universal reach, security-conscious upgrade paths, and account recovery in one architecture. Compare the platforms that ship this pattern out of the box in our OTP API providers comparison.
Implementation Checklist for African Deployments
Before you ship, verify the following.
- Direct carrier routes for SMS in every market you serve — MTN, Vodafone, AirtelTigo, Glo, 9mobile, Orange.
- Short OTP expiration windows — five minutes is a sensible default. See OTP expiration and rate limiting best practices.
- Rate limiting per user, per IP, and per phone number to block enumeration.
- Fraud monitoring for SMS pumping signals — unusual destination prefixes, single-recipient bursts.
- Channel-failover logic — if SMS fails delivery within 60 seconds, automatically retry on Voice or Email.
- TOTP support behind an account-settings toggle for users who want it.
If you are still mapping your stack, our step-by-step OTP API setup tutorial walks through the full integration end to end.
Frequently Asked Questions
Is SMS OTP secure?
SMS OTP is secure enough for low-to-medium risk flows and effective against the vast majority of attacks. Google’s data shows SMS-based two-step verification blocks 100% of automated attacks, 96% of bulk phishing attacks, and roughly three-quarters of targeted attacks. For high-value accounts, layer in TOTP or push as an upgrade.
What is the difference between SMS OTP and an authenticator app?
SMS OTP delivers a code over the mobile carrier network — universal device reach, no app install. An authenticator app generates a code locally on the device, offline, every 30 to 60 seconds — with no SMS in the chain. SMS optimises for reach. Authenticator apps optimise for resistance to SIM-swap and SS7 attacks.
Is email OTP safer than SMS?
Neither is universally safer. Email OTP avoids SIM-swap risk but introduces email-account compromise risk. SMS OTP avoids inbox-compromise risk but is exposed to SIM swap on high-value accounts. Pick the channel that matches the risk tier of the action and the device your user actually owns.
Why do banks still use SMS OTP?
Universal device reach. Banks need every customer to authenticate — including feature-phone users — and SMS is the only channel that meets that bar. Direct carrier connections also give banks the delivery reliability and audit trail their compliance teams require.
What is TOTP and how does it work?
TOTP stands for time-based one-time password. The authenticator app and your server share a secret. Both compute a six-digit code from that secret plus the current time, refreshing every 30 to 60 seconds. The code is generated locally on the device with no network round-trip — that is why TOTP works offline.
Should I support multiple OTP channels?
Yes. Layer SMS as the default, TOTP as an opt-in upgrade, and email as a fallback. This covers universal reach, security upgrades, and account recovery in one architecture — and lets you route each flow to the channel that matches its risk tier.
Ship Multi-Channel OTP Without Rebuilding Your Stack
The right OTP channel is not a single answer — it is a layered architecture matched to your users’ devices and the risk tier of each action.
Arkesel gives you that layering in one platform. Direct carrier connections to MTN, Vodafone, and AirtelTigo deliver SMS OTPs reliably at a 99.9% delivery rate. VoiceConnect handles your IVR fallback. The OTP API ties it together for developers.
Ready to build? Create a free Arkesel account and ship your first multi-channel OTP flow today. For current rates, see the Arkesel pricing page.