Artificially generated OTP traffic is the silent line item that drains your SMS budget while your real signups stay flat. Bots hit your verification endpoint, your provider sends real messages to attacker-controlled numbers, and you pay the bill. This guide is your developer-facing playbook for SMS pumping prevention: the exact log signals to monitor, runnable SMS pumping detection patterns, runnable burst detectors, and the Africa-specific OTP fraud prevention plays no global competitor covers.
What Is Artificially Generated OTP Traffic?
Artificially generated OTP traffic — also called Artificially Inflated Traffic (AIT) or SMS pumping — is a scheme where attackers exploit your OTP and verification endpoints to generate massive volumes of fake SMS messages. The messages route to premium-rate phone numbers the attacker controls. Every message you send earns them money.
It’s not a theoretical risk. AIT fraud cost brands $1.16 billion in 2023, according to an Enea white paper cited by Sinch. Elon Musk revealed that Twitter lost $60 million per year to SMS pumping from 390 telecom operators before the company cut off SMS-based two-factor authentication entirely, as reported by Benzinga.
Your OTP endpoint is the front door. If it’s unprotected, attackers will walk through it.
How AIT Attacks Work: The Attack Chain
Every SMS pumping attack follows the same pattern. Understanding the chain is the first step to breaking it.
Step 1: Reconnaissance
The attacker identifies a web or mobile application with an SMS-triggered endpoint — a signup form, password reset, phone verification, or any flow that sends an OTP. They test the endpoint to determine rate limits, geographic restrictions, and whether a CAPTCHA exists.
Step 2: Bot-Driven OTP Requests
Automated scripts submit phone numbers to the OTP endpoint at high volume. The numbers belong to premium-rate ranges or international destinations where the attacker has a revenue-sharing agreement with a telecom operator.
Step 3: Message Routing and Revenue Collection
Your OTP provider delivers the messages. Each SMS incurs a termination fee. The telecom operator on the receiving end collects the fee — and shares a portion with the attacker.
Step 4: Scale and Repeat
The attacker rotates IP addresses, phone number ranges, and geographic targets. A single compromised endpoint can generate thousands of fraudulent OTP requests per hour. Your SMS bill spikes. Your delivery metrics collapse.
Here’s what that looks like in practice:
Attacker's Bot Network
│
▼
Your Signup Form → OTP API Endpoint → SMS Provider
│ │
│ ▼
│ Premium-Rate Numbers
│ │
│ ▼
│ Telecom Operator
│ │
│ ▼
│ Revenue Share → Attacker
│
▼
You Pay the Bill
The entire chain can execute in seconds. By the time you notice the spike in your SMS dashboard, the damage is done.
The Cost of Artificially Inflated Traffic in 2026
The industry-wide numbers explain why every serious OTP provider now treats AIT as a tier-one platform risk.
Juniper Research projects total messaging fraud losses at $80.5 billion in 2025, declining to $71 billion in 2026 as carriers and providers tighten controls. AIT specifically is estimated to account for roughly 5% of all worldwide A2P SMS traffic, according to Group-IB’s analysis. The independent telecom-industry trade press confirms the Twitter/X loss at roughly $60 million per year across 390 telcos — a public reminder that even the largest platforms are not immune.
The direction is clear: regulators are pushing back, providers are deploying detection, and platform vendors are codifying defenses. AWS End User Messaging now ships built-in features to combat artificially inflated traffic — but the burden of detection still lives in your application logs.
How to Detect SMS Pumping in Your Logs
Most “OTP fraud” guides skip the part developers actually need for SMS pumping detection: what does artificially generated OTP traffic look like in your logs, and what thresholds should trigger an alert?
These five signals, monitored together, detect the vast majority of pumping campaigns within minutes of onset.
| Signal | What to Measure | Suspicious Threshold | Confidence |
|---|---|---|---|
| Burst rate | OTP requests per minute per endpoint | >10x your 7-day rolling baseline | High |
| Verify-to-send ratio | OTP verifications / OTP sends, rolling 1-hour window | Below 30% (healthy: 60-85%) | Very high |
| Country-code anomaly | OTP sends to country codes outside your top 5 | Any sudden spike to an unused country code | High |
| IP / device clustering | Unique phone numbers per IP per hour | >5 numbers from one IP in 60 minutes | High |
| First-message-fail rate | OTPs returning operator-side delivery failures | Sudden rise alongside cost spike | Medium |
The verify-to-send ratio is the most reliable single metric. Legitimate users verify. Bots do not. A drop from 70% to 25% over an hour is artificially generated OTP traffic, full stop.
Burst-Detection Pseudocode (Language-Agnostic)
The pattern below is the canonical sliding-window detector developers can adapt in any stack. Run it on every incoming OTP request and flag the request before the SMS leaves your provider.
# Canonical burst detector for artificially generated OTP traffic
# Inputs: incoming OTP request (phone, ip, device_id, country_code, timestamp)
# State: rolling counters keyed by (phone, ip, device) over a sliding window
function detectPumping(request):
# 1. Update sliding-window counters (last 60 minutes)
increment_counter("otp:phone:" + request.phone, window=3600s)
increment_counter("otp:ip:" + request.ip, window=3600s)
increment_counter("otp:device:" + request.device_id, window=3600s)
increment_counter("otp:cc:" + request.country_code, window=3600s)
# 2. Compute pumping signals
burst_score = counter("otp:ip:" + request.ip) # bot bursts cluster on IPs
geo_score = counter("otp:cc:" + request.country_code) / baseline_for(request.country_code)
fanout_score = unique_phones_per_ip(request.ip, window=3600s)
verify_ratio = verified_count(window=3600s) / sent_count(window=3600s)
# 3. Decide
if burst_score > 10 return BLOCK # > 10 OTPs per IP per hour
if fanout_score > 5 return BLOCK # > 5 unique numbers per IP per hour
if geo_score > 5 return CHALLENGE # 5x the normal volume for this country code
if verify_ratio < 0.30 and sent_count(window=3600s) > 50: return GLOBAL_THROTTLE
return ALLOW
The core idea: maintain rolling counters per identifier, compute a verify-to-send ratio in parallel, and act on the first signal that crosses its threshold. Block, challenge with CAPTCHA, or globally throttle — never silently allow.
Node.js Implementation with Redis
For a production-ready version, use Redis for distributed rate-limit counters and tie the decision into your existing OTP send path.
const Redis = require('ioredis');
const redis = new Redis();
const OTP_LIMITS = {
phone: { max: 5, windowSeconds: 3600 },
ip: { max: 10, windowSeconds: 3600 },
device: { max: 5, windowSeconds: 3600 }
};
async function checkRateLimit(type, identifier) {
const key = `otp_limit:${type}:${identifier}`;
const current = await redis.incr(key);
if (current === 1) {
await redis.expire(key, OTP_LIMITS[type].windowSeconds);
}
return current <= OTP_LIMITS[type].max;
}
async function handleOtpRequest(req, res) {
const { phoneNumber } = req.body;
const clientIp = req.ip;
const deviceId = req.headers['x-device-id'] || 'unknown';
const checks = await Promise.all([
checkRateLimit('phone', phoneNumber),
checkRateLimit('ip', clientIp),
checkRateLimit('device', deviceId)
]);
if (checks.some(allowed => !allowed)) {
return res.status(429).json({
error: 'Too many OTP requests. Try again later.'
});
}
const otpResponse = await sendOtp(phoneNumber);
return res.json({ success: true, message: 'OTP sent.' });
}
Python (Flask + Redis) Equivalent
import redis
from flask import Flask, request, jsonify
app = Flask(__name__)
r = redis.Redis()
OTP_LIMITS = {
"phone": {"max": 5, "window": 3600},
"ip": {"max": 10, "window": 3600},
"device": {"max": 5, "window": 3600},
}
def check_rate_limit(limit_type, identifier):
key = f"otp_limit:{limit_type}:{identifier}"
current = r.incr(key)
if current == 1:
r.expire(key, OTP_LIMITS[limit_type]["window"])
return current <= OTP_LIMITS[limit_type]["max"]
@app.route("/api/otp/send", methods=["POST"])
def send_otp_endpoint():
phone_number = request.json.get("phone_number")
client_ip = request.remote_addr
device_id = request.headers.get("X-Device-Id", "unknown")
if not all([
check_rate_limit("phone", phone_number),
check_rate_limit("ip", client_ip),
check_rate_limit("device", device_id),
]):
return jsonify({"error": "Too many OTP requests."}), 429
otp_response = send_otp(phone_number)
return jsonify({"success": True, "message": "OTP sent."})
Rate-Limit Configuration Pattern
Three limits in parallel, with exponential backoff, defeats the economics of most pumping campaigns:
otp_rate_limits:
per_phone_number:
max_requests: 5
window_seconds: 3600
backoff: exponential # 30s -> 60s -> 5m -> 30m
per_ip_address:
max_requests: 10
window_seconds: 3600
backoff: exponential
per_device_fingerprint:
max_requests: 5
window_seconds: 3600
backoff: exponential
global_circuit_breaker:
trip_when_verify_to_send_ratio_below: 0.30
minimum_sample_size: 50
action: throttle_globally_for_minutes: 15
For a deeper look at the rate-limiting layer, including OTP TTL design, retry windows, and provider-side controls, read our companion guide on rate limiting and OTP expiration best practices. The Arkesel API exposes these controls natively — see the Arkesel developer documentation for the per-endpoint rate-limit headers and recommended request budgets.
Warning Signs Your OTP Endpoint Is Being Pumped
You don’t need sophisticated monitoring to spot SMS pumping. These signals appear fast — if you know where to look.
Traffic Volume Spikes
A sudden surge in OTP requests that doesn’t correlate with user activity. Your registration rate hasn’t changed, but OTP sends jumped 500% overnight. That’s not organic growth.
Unusual Geographic Distribution
OTP requests suddenly targeting countries where you have no users. If your product serves Ghana and Nigeria but your OTP logs show hundreds of requests to premium-rate numbers in Eastern Europe or Southeast Asia, you’re under attack.
Low Verification Completion Rates
This is the most reliable signal. In a legitimate flow, most OTPs get verified — users enter the code to complete signup or login. SMS pumping generates OTPs that nobody verifies. If your send-to-verify ratio drops below 30%, investigate immediately.
Concentrated Request Patterns
Multiple OTP requests from the same IP address, the same device fingerprint, or sequential phone number ranges within a short window. Legitimate users don’t request 50 OTPs from the same IP in 10 minutes.
SMS Cost Anomalies
Your monthly SMS spend doubles or triples without a corresponding increase in conversions. Check your provider’s billing dashboard for cost spikes in specific country codes.
Prevention Strategies: A Multi-Layered Defense
No single technique stops SMS pumping. Attackers adapt. Effective OTP fraud prevention needs multiple layers so that bypassing one still triggers another.
Geographic Restrictions (Country Allowlists)
If your application serves users in Ghana, Nigeria, and South Africa, there’s no reason to send OTPs to numbers in the Maldives or Tonga.
Implement a country allowlist that blocks OTP delivery to any country code outside your operating regions. This single control eliminates entire categories of premium-rate fraud.
const ALLOWED_COUNTRY_CODES = [
'+233', // Ghana
'+234', // Nigeria
'+27', // South Africa
'+254', // Kenya
'+225', // Cote d\'Ivoire
];
function isAllowedCountry(phoneNumber) {
return ALLOWED_COUNTRY_CODES.some(
code => phoneNumber.startsWith(code)
);
}
Update the allowlist as you expand to new markets — but default to deny. Every unblocked country code is an open door for pumping attacks.
CAPTCHA and Proof-of-Work Before OTP Trigger
Place a CAPTCHA challenge before the OTP request — not after. If the bot can trigger the SMS without solving a challenge, the CAPTCHA is useless.
Google reCAPTCHA v3, hCaptcha, and Cloudflare Turnstile all work as invisible challenges that add minimal friction for real users while blocking automated scripts.
The key: the CAPTCHA must gate the API call that triggers SMS delivery. Placing it on the frontend form but not validating server-side leaves the OTP endpoint exposed to direct API calls.
Phone Number Intelligence
Not all phone numbers are equal. Before sending an OTP, verify the number’s legitimacy:
- Carrier lookup: Identify whether the number belongs to a real mobile carrier or a virtual/VoIP provider. Premium-rate numbers used in pumping attacks have distinct carrier signatures.
- Disposable number detection: Online services sell temporary phone numbers for receiving SMS. Flag or block these.
- Number type validation: Confirm the number is a mobile number, not a landline or toll-free number being abused for revenue generation.
Arkesel’s Phone Number Verification service validates number type and carrier information before you spend money sending an OTP to a fraudulent destination.
Anomaly Detection and Real-Time Monitoring
Build dashboards that track these metrics in real time:
- Send-to-verify ratio: The percentage of OTPs that get successfully verified. Healthy range: 60-85%. Below 30% signals pumping.
- OTP requests per country per hour: Sudden spikes in unexpected countries need immediate investigation.
- Cost per successful verification: If this metric rises sharply while conversion stays flat, you’re paying for fraudulent traffic.
- Unique phone numbers per IP: Legitimate users don’t submit dozens of different phone numbers from a single IP address.
Set automated alerts on these thresholds. When the send-to-verify ratio drops below 40% or cost-per-verification doubles, trigger automatic geographic blocks and increased rate limiting.
Cost Caps and Alerting Thresholds
Configure hard spending limits with your SMS provider. A monthly cap that triggers an alert at 80% and pauses delivery at 100% prevents runaway costs during an active attack.
This isn’t about limiting your business. It’s about limiting your exposure. A capped monthly budget means a successful pumping attack costs you what you set — not an unbounded surprise on your invoice.
Most enterprise SMS providers support budget controls. If yours doesn’t, that’s a reason to switch. For a deeper comparison of which providers ship the strongest fraud controls out of the box, see our OTP API provider comparison for 2026.
Africa-Specific SMS Pumping Patterns
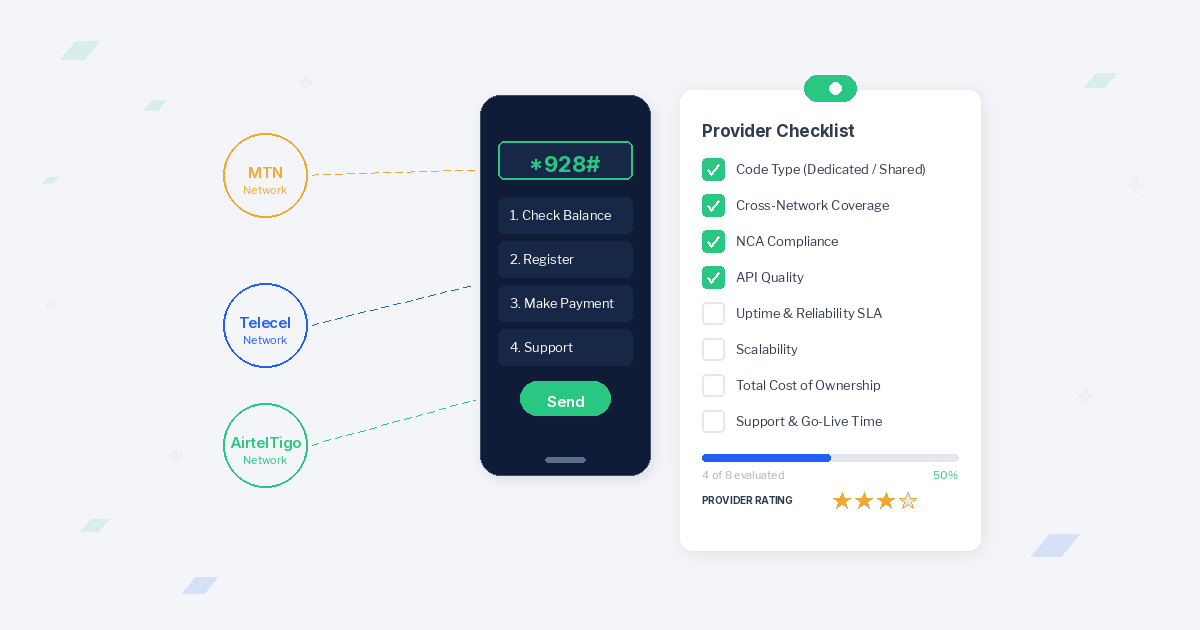
Global guides treat artificially generated OTP traffic as a US/EU problem. African developers shipping into MTN, Vodafone, and AirtelTigo footprints see a different threat surface — and need a different defense posture.
The regional context is real. Security Focus Africa flags Africa among the key target regions for SMS pumping fraud alongside APAC and MENA, with South Africa specifically called out. Three patterns matter more on this continent than anywhere else.
1. Cross-Border Pumping via Inter-Operator Routes
African telecom routes hop across multiple operators before terminating. An OTP sent from a Lagos signup form can transit two or three intermediaries before reaching the destination handset. Each hop is a potential collusion point — and a fraud route that doesn’t show up on standard country-code allowlists.
The defense: prefer providers with direct connections into the destination networks. Direct termination removes the intermediary leg where pumping arrangements typically live.
2. Premium-Rate Number Ranges on Local Carriers
MTN, Vodafone, and AirtelTigo each maintain premium-rate number ranges for legitimate revenue-share services. Attackers acquire or spoof numbers in these ranges and point your OTP endpoint at them. Because the numbers are technically valid mobile numbers on real local carriers, naive carrier-lookup checks let them through.
The defense: number-type validation that distinguishes consumer mobile ranges from premium-rate ranges within the same carrier. This requires a provider with carrier-level intelligence, not just country-code logic.
3. Bursty Patterns on Local-Holiday Schedules
Pumping campaigns targeting African endpoints frequently spike around local payday cycles and public holidays, when legitimate signup volume is also elevated — masking the burst inside a real spike. The verify-to-send ratio is the only signal that survives this overlap. Real users verify; bots don’t.
Why Direct Network Connections Matter for African OTP Delivery
Arkesel maintains direct mobile network connections with MTN, Vodafone, and AirtelTigo. That changes the threat model:
- Visibility into carrier-level routing — premium-rate destinations are identifiable before delivery, not after the invoice.
- No fraud-prone intermediary hops — the OTP terminates directly on the destination network, eliminating the cross-border collusion window.
- Real-time anomaly monitoring across the carrier edge — burst patterns hitting one network are visible to platform defenses immediately, not lagged through middleware.
For enterprises building OTP flows for African users, the provider’s network topology is part of the fraud model. See how Arkesel’s direct network connections deliver OTPs without the AIT exposure of indirect routes via the Arkesel Phone Number Verification service or the Arkesel SMS Platform.
How Pumping Hits Fintech and Banking OTPs
Artificially generated OTP traffic is not just a billing problem — it’s a transaction-security problem. When attackers can exhaust an OTP endpoint, two downstream effects hit fintech and banking workloads hard:
- Legitimate authentication degrades. Aggressive rate limiting during a live attack can throttle real customers trying to complete a transaction.
- Detection budgets compete. Fraud teams chasing AIT spikes are not chasing account takeover patterns at the same time.
For regulated workloads, the OTP layer needs both pumping resistance and transaction-grade reliability. The companion guide on OTP for fintech banking transaction security covers the compliance, channel-redundancy, and audit-log requirements that sit on top of the pumping defenses in this guide.
How Arkesel Protects Against SMS Pumping
Arkesel’s SMS Platform is built with fraud prevention at the infrastructure level — not bolted on as an afterthought.
Delivery analytics and anomaly detection. Real-time delivery tracking exposes suspicious patterns the moment they emerge. Sudden spikes in send volume, drops in verification completion, or unusual geographic distribution trigger automatic flags.
Carrier intelligence. Direct mobile network connections with MTN, Vodafone, and AirtelTigo give Arkesel visibility into carrier-level routing. Premium-rate number detection and carrier validation happen before message delivery — blocking fraudulent destinations at the source.
Phone Number Verification. Validate number type, carrier, and status before sending. Stop OTPs from reaching disposable numbers, VoIP lines, or premium-rate ranges that exist solely to collect termination fees.
Real-time monitoring with Kova IQ. Track OTP delivery patterns, verification success rates, and cost anomalies across all channels through a single analytics dashboard. Kova IQ turns raw delivery data into actionable fraud signals — so you detect attacks in minutes, not days.
Geographic controls. Restrict OTP delivery to specific country codes through your Arkesel dashboard. No API changes required. Enable a country when you expand there; block everything else by default.
For teams building OTP systems from scratch, Arkesel’s API delivers generation, sending, and verification with built-in rate limiting and fraud signals. Create a free account to test the OTP flow in your staging environment.
The Regulatory Landscape: Industry Response to AIT
The industry is fighting back on SMS pumping prevention — but the burden still falls on you to protect your endpoints.
Twitter/X’s precedent. After discovering 390 telecom operators were exploiting its 2FA system, Twitter removed free SMS-based authentication in March 2023 — as documented by CommsRisk. The move demonstrated that even the largest platforms aren’t immune, and that drastic action sometimes follows years of unchecked fraud.
Evolving AIT tactics in 2026. According to Twilio’s March 2026 fraud update, AIT is no longer limited to OTP flows. Attackers now inflate traffic through app download links, surveys, and promotional campaign endpoints. Fraud automation tools mimic legitimate user behavior with increasing sophistication, making traditional detection harder.
Telecom collaboration. Leading providers are establishing joint anti-fraud protocols with mobile network operators. The goal: shared intelligence on known premium-rate fraud ranges and real-time blocking at the carrier level. Africa-focused providers with direct carrier connections — like those maintaining relationships with MTN, Vodafone, and AirtelTigo — are better positioned to deliver these defenses.
The zero-trust communication model. The emerging standard: treat every OTP request as potentially fraudulent until proven otherwise. Verify the requester (CAPTCHA), validate the destination (carrier lookup), limit the volume (rate limiting), and monitor the outcome (verification completion tracking).
For a broader view of OTP security beyond fraud prevention, including SIM swap protection and delivery channel security, read the OTP security best practices guide.
Implementation Checklist
Use this checklist to audit your OTP endpoint against artificially generated OTP traffic:
- Burst detector active — Sliding-window counters per phone, IP, and device, with verify-to-send ratio in parallel
- Rate limiting active — Per phone number, per IP, per device fingerprint with exponential backoff
- CAPTCHA gates the OTP trigger — Server-side validation, not just frontend
- Country allowlist configured — Only countries where you have real users
- Phone number validation enabled — Carrier lookup and number type check before sending
- Spending cap set — Monthly budget with alerts at 80% and hard stop at 100%
- Verification ratio monitored — Alerting when send-to-verify drops below 40%
- Geographic anomaly detection — Automatic alerts for unexpected country spikes
- Premium-rate range detection — Carrier-level intelligence within each destination network, not just country-code filtering
- Provider fraud tools enabled — Activate every built-in fraud protection your SMS provider offers
No single control stops a determined attacker. But layered defenses make the attack economics unfavorable — and that’s how you win.
If you encounter delivery failures after deploying these controls, the OTP API troubleshooting guide covers how to diagnose whether the issue is a false positive from your fraud rules or a legitimate delivery problem.
Frequently Asked Questions
What is artificially generated OTP traffic?
Artificially generated OTP traffic is fraudulent SMS volume created by bots hitting an OTP endpoint, sending real messages to attacker-controlled premium-rate numbers. The attacker earns a share of the termination fee on every message you pay to send. It’s also called Artificially Inflated Traffic (AIT) or SMS pumping.
How do you detect SMS pumping in your logs?
Monitor five signals together: burst rate per IP (>10x baseline), verify-to-send ratio (below 30% is suspicious), country-code anomaly (sudden volume to an unused country code), unique phone numbers per IP per hour (>5 numbers from one IP), and first-message-fail rate. The verify-to-send ratio is the single most reliable signal — real users verify, bots don’t.
What is the difference between SMS pumping and SMS spam?
SMS pumping (AIT) exploits your OTP endpoint to send messages to premium-rate numbers the attacker controls — you pay for every message. Regular SMS spam sends unwanted marketing messages to real users. With pumping, the attacker profits from the delivery fees you’re charged, not from the message content reaching anyone.
How much does SMS pumping cost businesses annually?
AIT fraud cost brands $1.16 billion in 2023, according to research cited by Sinch. Juniper Research projects total messaging fraud losses at $80.5 billion in 2025, declining to $71 billion in 2026. Individual company losses vary widely — Twitter reported $60 million per year before cutting off SMS-based 2FA.
How can African businesses defend against SMS pumping?
Three controls matter most for African deployments: pick a provider with direct network connections to MTN, Vodafone, and AirtelTigo (eliminates cross-border collusion routes); deploy carrier-level number-type validation to distinguish consumer mobile ranges from premium-rate ranges within each local carrier; and monitor verify-to-send ratio in real time so payday and holiday spikes can’t mask a burst.
Talk to Arkesel About Fraud-Resistant OTP Delivery
Artificially generated OTP traffic is a solved problem when detection, rate limiting, and direct network routing run together. Arkesel delivers all three — backed by direct mobile network connections to MTN, Vodafone, and AirtelTigo and real-time anomaly monitoring through Kova IQ.
Talk to Arkesel about fraud-resistant OTP delivery on direct African network connections, or sign up for a free account to start testing the OTP flow today.
This post is part of the Implementing OTP APIs: Modern Authentication Guide cluster. Continue the series with rate limiting and OTP expiration best practices, the OTP API provider comparison for 2026, or our deep dive on OTP for fintech banking transaction security.